A recent post in radioscanner (my nickname is "ansanto" there), and some interesting discussions with a friend of mine, gave me the opportunity to study that signal and deepen the theme that is dealt with by MIL 188-220. In particular, the signal in question (courtesy by KarapuZ) concerns a transmission with link encryption provided by external COMSEC devices, in accordance with what is reported in the Appendix D of the cited standard, ie "transmission frame structure in either external and embedded COMSEC modes".
In short, in external COMSEC transmission frame the clear-text (not encrypted) part of the transmission frame is the "COMSEC Preamble", depicted below, which consists of the subfields:
a. COMSEC Bit Synchronization
b. COMSEC Frame Synchronization
c. Message Indicator - MI or, better, Initialization Vector - IV (1)
The COMSEC Frame Synchronization subfield is used to provide a framing signal indicating the start of the encoded MI to the receiving station. This subfield is 465 bits long, consisting of 31 Phi-encoded bits. The Phi patterns are a method of redundantly encoding data bits. The logical data bits 1 and 0 are encoded as shown in figure.
The Message Indicator subfield (MI) contains the COMSEC-provided MI, a stream of random bits that are redundantly encoded using Phi patterns.
Alternatively, in the embedded COMSEC transmission frame the clear-text part, depicted below, is composed of the following components:
a. Phasing
b. Frame synchronization (Standard Frame Sync or Robust Frame Sync)
c. Robust Frame Format (RCP only)
d. Message Indicator/ Initialization Vector
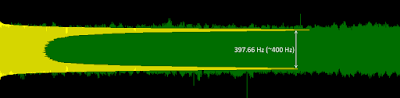
Back to the signal, it was heard by KarapuZ in the 33 MHz band and it is a GFSK modulation at a rate of 16000 Baud that can be easily processed using SA (Fig. 1).
 |
| Fig. 1 |
 |
| Fig. 2 |
Since 188-220 is based on the VINSON algorithm, the used encryption is presumably KY-57 and taking into account the band where it was listened... everything points to the SINCGARS radio (Single Channel Ground and Airborne Radio System) [1].
By the way, a dear friend of mine sent me a recording but once demodulated it uses 16 bits encoding patterns frames instead of 15 bits ones (Fig. 3). "I guess it is some modern crypto using a backwards compatibility mode, the clue is that it could be KY-99 that is the replacement for KY-57 in SINCGARS, but that point is unconfirmed. More signals and work will be necessary to clarify these points", my friend says.
 |
| Fig.3 |
It is interesting to see how NATO KG-84 encryption relates to 188-220 Appendix D (Fig. 4).
KG-84 is similar to the emebedded COMSEC transmission frame, although the 64-bit pattern of KG-84 Standard Frame sync
KG-84 is similar to the emebedded COMSEC transmission frame, although the 64-bit pattern of KG-84 Standard Frame sync
1111101111001110101100001011100011011010010001001100101010000001
is different from the patterns reported in Appendix D for Standard and Robust Frame sync. Moreover, the Message Indicator is not encoded using the Phi 15 bits, although it is redundantly encoded. That's probably ok since KG-84 is based on SAVILLE algorithm and 188-220 is VINSON based. Note as in some KG-84 "detectors" the Standard Frame sync is termed as "SYNC" and the MI data as "Initialization vectors". |
| Fig. 4 - NATO KG-84 encryption and 188-220 embedded COMSEC |
The Turkish-Mil FSK, also using KG-84, deserves aside consideration (Fig. 5). Perhaps they encode the Mesage Indicator field using Golay and do not use redundant n-bit encoding, but it's only IMO. However "the encoding with Phi patterns is used for backward compatibility", 188-220 says.
(1) An Initialization Vector (IV) or starting variable (SV) is a block of bits that is used by several modes to randomize the encryption and hence to produce distinct ciphertexts even if the same plaintext is encrypted multiple times, without the need for a slower re-keying process. An initialization vector has different security requirements than a key, so the IV usually does not need to be secret. However, in most cases, it is important that an initialization vector is never reused under the same key.[2] [3]
 |
| Fig. 5 - Turkish-Mil FSK and 188-220 embedded COMSEC |
(1) An Initialization Vector (IV) or starting variable (SV) is a block of bits that is used by several modes to randomize the encryption and hence to produce distinct ciphertexts even if the same plaintext is encrypted multiple times, without the need for a slower re-keying process. An initialization vector has different security requirements than a key, so the IV usually does not need to be secret. However, in most cases, it is important that an initialization vector is never reused under the same key.[2] [3]
Please notice that just starting with this post I will use the term "Initialization Vector" to indicate the (repeated) pseudo-random sequence that is used to synch the receive crypto equipment.
[1] http://www.cryptomuseum.com/radio/sincgars/
[1] http://www.cryptomuseum.com/radio/sincgars/